The Proxmox web GUI is served by Proxmox’s new event driven API server called PVE Proxy. The default settings for the Proxmox web GUI is to listen on port 8006 for incoming HTTPS connections.
The following tutorial will show you how to use Nginx to reverse proxy the PVE Proxy application to do the following:
- Redirect HTTP requests to use the HTTPS protocol.
- Add your own certificate to use for HTTPS.
- Listen on the standard HTTPS port (port 443).
The following steps show how to use Nginx to reverse Proxy Proxmox’s web GUI. If you would prefer to use Apache, please see my other blog post.
The first step is to make sure you have Nginx installed on the machine, or virtual instance, that you are going to use. You can install Nginx directly on the Proxmox host however, I prefer to keep the host software as standard as possible and run all additional applications in OpenVZ containers.
Create a shell session on the machine you would like to use and use apt-get to install Nginx.
apt-get install nginx
Make sure you have an SSL certificate and key pair on your server. See my OpenSSL certificate cheat sheet for more information.
We now need to specify the configuration for Nginx. Remove the existing site configuration and create a new configuration file called proxmox-gui. You can call this file whatever you wish, but you will also need to use the same name in the below steps.
rm -f /etc/nginx/sites-enabled/default
vi /etc/nginx/sites-enabled/proxmox-gui
Add the below text to your proxmox-gui file. You will need to substitute some of the settings with your own values:
- ssl_certificate – this should point to your SSL certificate to use for signing the SSL traffic.
- ssl_certificate_key – is this key which matches the above certificate.
- server – this is the IP and port of your Proxmox server. If you have installed Nginx on the same host as the Proxmox web GUI then you could use https://localhost:8006 here.
upstream proxmox {
server 10.10.10.10:8006;
}
server {
listen 80 default_server;
rewrite ^(.*) https://$host$1 permanent;
}
server {
listen 443;
server_name _;
ssl on;
ssl_certificate /etc/nginx/ssl/cert.pem;
ssl_certificate_key /etc/nginx/ssl/key.pem;
proxy_redirect off;
location / {
proxy_pass https://proxmox;
}
}
If you have multiple Proxmox servers in a cluster, it would make sense to use load balancing in Nginx. We don’t really want to use this feature to spread the load, because usually the traffic will be very light – we want to use it so that if one node in the cluster is down, Nginx will automatically try a different node in the cluster.
To add load balancing, add your additional servers in the upstream proxmox code section. For example:
upstream proxmox {
server 10.10.10.10:8006;
server 10.10.10.11:8006;
server 10.10.10.12:8006;
}
We need to link the newly created config file so that Nginx can load it.
ln -sf /etc/nginx/sites-available/proxmox-gui /etc/nginx/sites-enabled/
The last step is to restart Nginx web server to pick up the new settings.
service nginx restart
Your Proxmox web GUI should now be available on the IP address of your Nginx server on the HTTPS protocol.
 It’s never been easier to set up your own Git server to host your own git repositories for your projects. Thanks to people like the folks over at
It’s never been easier to set up your own Git server to host your own git repositories for your projects. Thanks to people like the folks over at 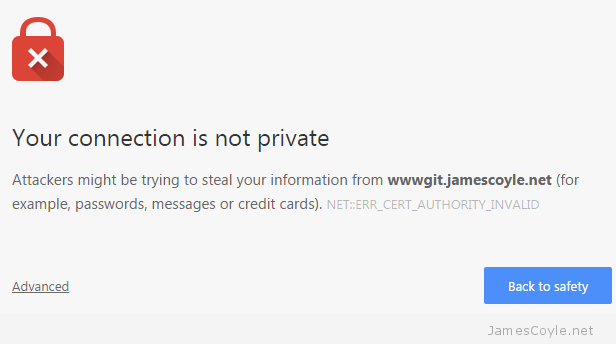
 These commands cover the basics of OpenSSL and are valid for either Windows or Linux with the exception that paths may need to be corrected for the respective platform.
These commands cover the basics of OpenSSL and are valid for either Windows or Linux with the exception that paths may need to be corrected for the respective platform. Creating multiple SSL certificates for web servers and application can be a repetitive task. Generally speaking, when creating these things manually you would follow the below steps:
Creating multiple SSL certificates for web servers and application can be a repetitive task. Generally speaking, when creating these things manually you would follow the below steps: